BitViraj Technologies - Your Gateway to
Tomorrow's Innovations

Blockchain Security & Crypto Forensics: Transaction Analysis & Investigation Framework
Blockchain's immutability and transparency create a permanent forensic trail, but sophisticated obfuscation techniques require advanced investigative methods. This comprehensive guide covers security vulnerabilities, forensic methodologies, and investigative tools across major blockchain ecosystems.
Blockchain Security & Crypto Forensics
Transaction Analysis & Investigation Framework

Blockchain Security & Crypto Forensics: Transaction Analysis & Investigation Framework
Part 1: Blockchain Security Architecture & Vulnerabilities
Layer 1 (Consensus Layer) Threats – 51% Attacks
- Ethereum Classic: 51% attack cost: ~$550k (2020)
- Bitcoin Gold: Double-spend of $18M (2018)
- Current 51% attack costs (24h):
- Bitcoin: $6.8B (ASIC rental)
- Ethereum: $34B (staking equipment)
- Solana: $6.9M (stake concentration)
Smart Contract Layer Exploits (2020-2023)
Total Losses: $8.4B (2020-2023)
| Attack Vector | Losses | Percentage |
|---|---|---|
| Access Control Violations | $2.9B | 34.5% |
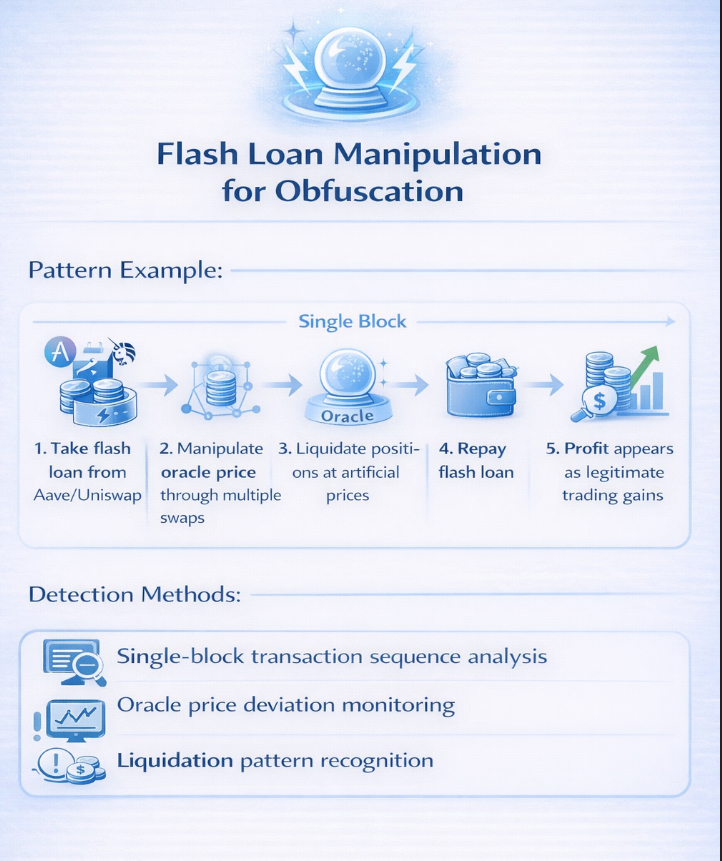
| Flash Loan Attacks | $1.5B | 17.9% |
| Reentrancy | $1.1B | 13.1% |
| Price Oracle Manipulation | $890M | 10.6% |
| Logic Errors | $720M | 8.6% |
Cross-Chain Security Landscape
Bridge Exploits (2021-2023): $2.5B+ stolen
- Ronin Bridge (Axie): $625M – Private key compromise
- Wormhole: $326M – Signature verification bypass
- Nomad Bridge: $190M – Improper initialization
- Harmony Horizon: $100M – Multi-sig compromise
- Poly Network: $611M (recovered) – Contract vulnerability
Common Bridge Attack Patterns:
- Signature verification flaws: 42%
- Administrative key compromise: 31%
- Validation logic errors: 18%
- Relayer manipulation: 9%
Part 2: Crypto Forensics Methodology
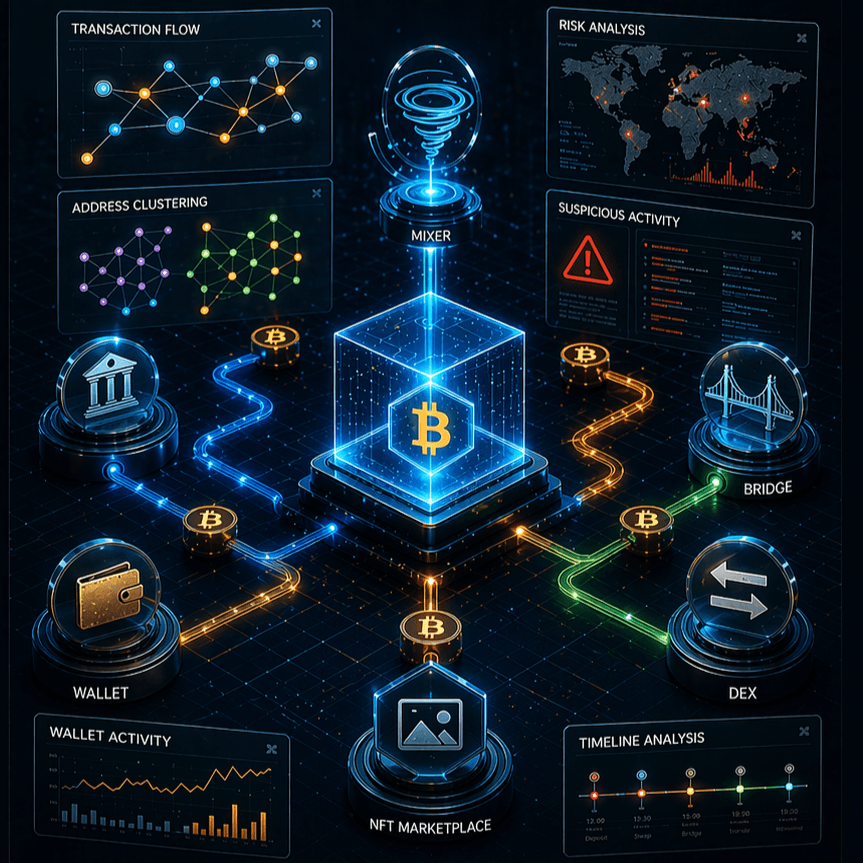
Investigative Framework (OSINT + Chain Analysis)
Phase 1: Initial Transaction Analysis
Tools: Etherscan, Blockchain.com, Solscan, Snowtrace. Data points: transaction hash, block height/timestamp, from/to addresses, value, gas used/price, input data, event logs.
Phase 2: Address Clustering & Entity Identification
Techniques: Common Input Ownership Heuristic, Change Address Detection, Address Reuse Patterns, Multi-input Transaction Analysis, Temporal Analysis.
Phase 3: Fund Flow Mapping
Visualization Tools: Maltego (Blockchain transforms), GraphSense, Elliptic AML Toolkit, TRM Labs Reactor, Chainalysis Reactor.
Phase 4: Behavioral Analysis & Attribution
Indicators: transaction timing patterns, gas price strategies, address generation patterns, DApp interactions. Attribution via IP correlation, metadata analysis, exchange KYC, subpoenas.
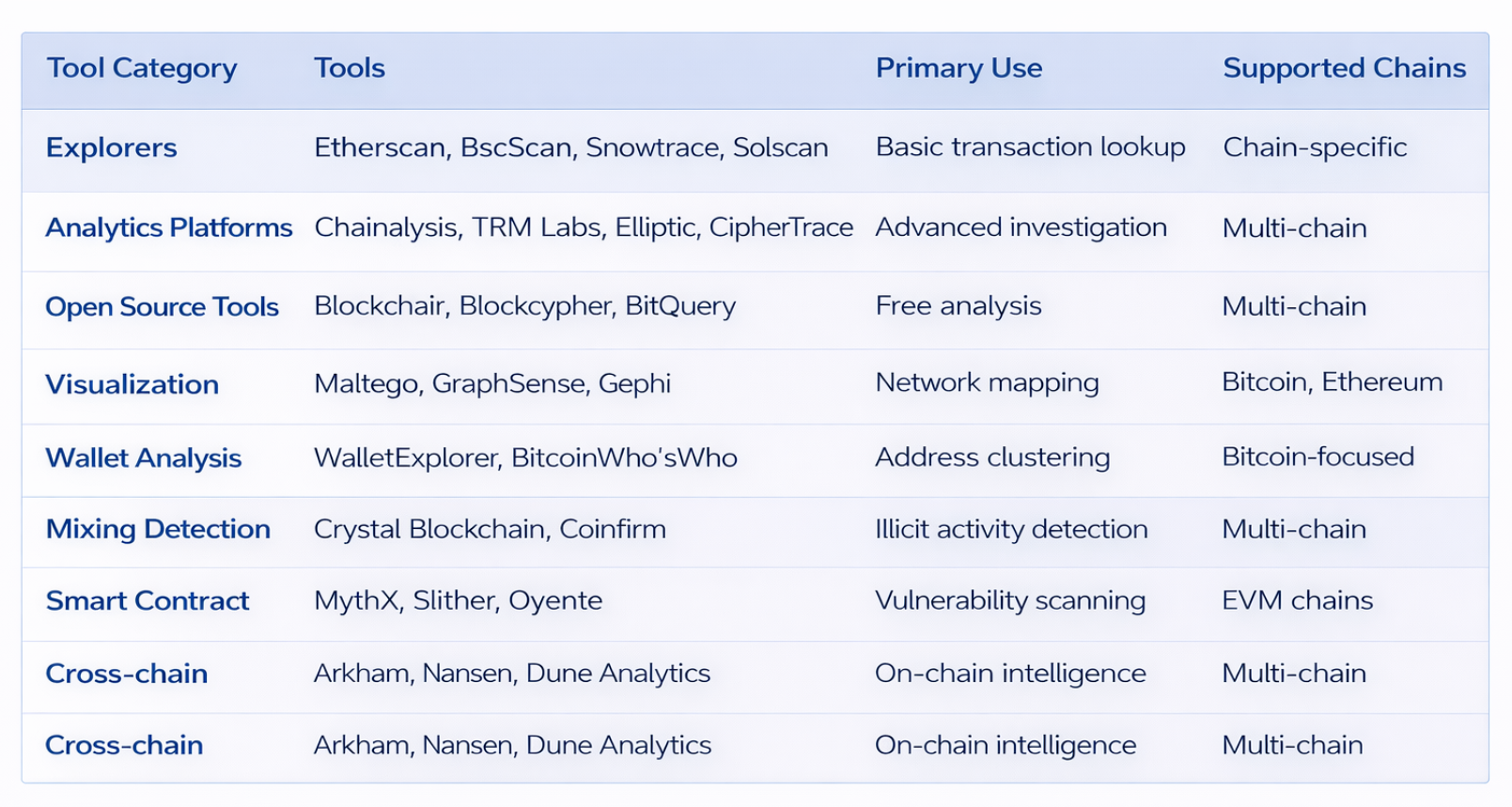
Forensic Tools Matrix
Part 3: Transaction Trail Analysis Techniques
De-anonymization Methods
Statistical Analysis – Transaction Graph Analysis:
- Degree centrality (connectedness)
- Betweenness centrality (intermediary role)
- Clustering coefficient (community detection)
- PageRank algorithm (importance scoring)
Heuristic-based Clustering:
- Multi-input Heuristic: If multiple inputs in a transaction, they're controlled by same entity
- Change Address Detection: Outputs not going to known addresses likely belong to sender
- Address Reuse: Entities reusing addresses create linkage points
- Peel Chain Detection: Series of transactions with small leftover amounts
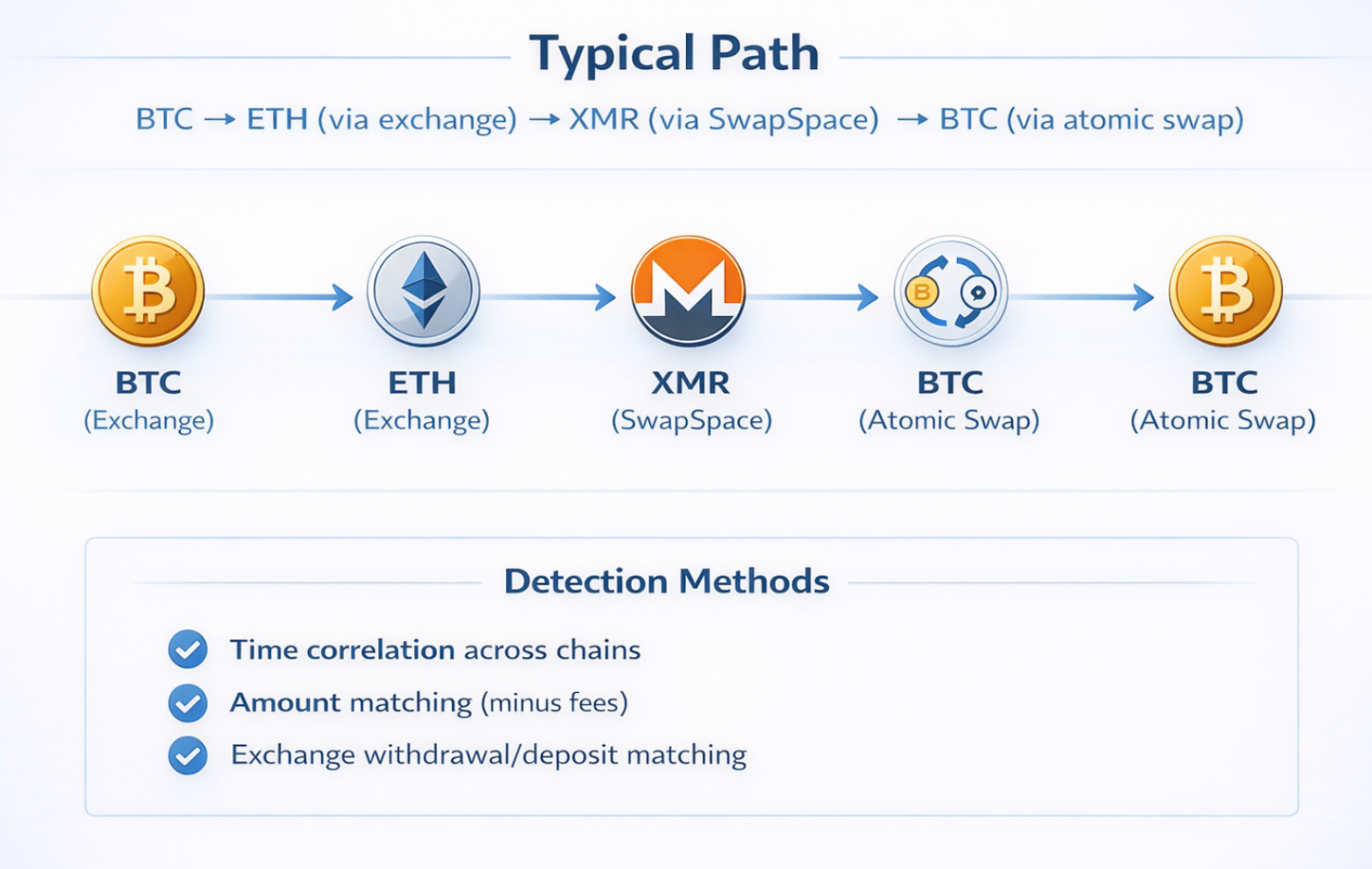
Privacy Coin Analysis – Monero (XMR)
Forensic Approaches: Temporal analysis, amount analysis, chain reaction, exchange correlation. Recent breakthrough: Fluffy Spider attack (2020) with 96% accuracy for ≥5 mixins.
Zcash (ZEC) Forensics
Investigation techniques: pool migration analysis (transparent↔shielded), metadata analysis (tx size, timing), known entity interaction patterns.
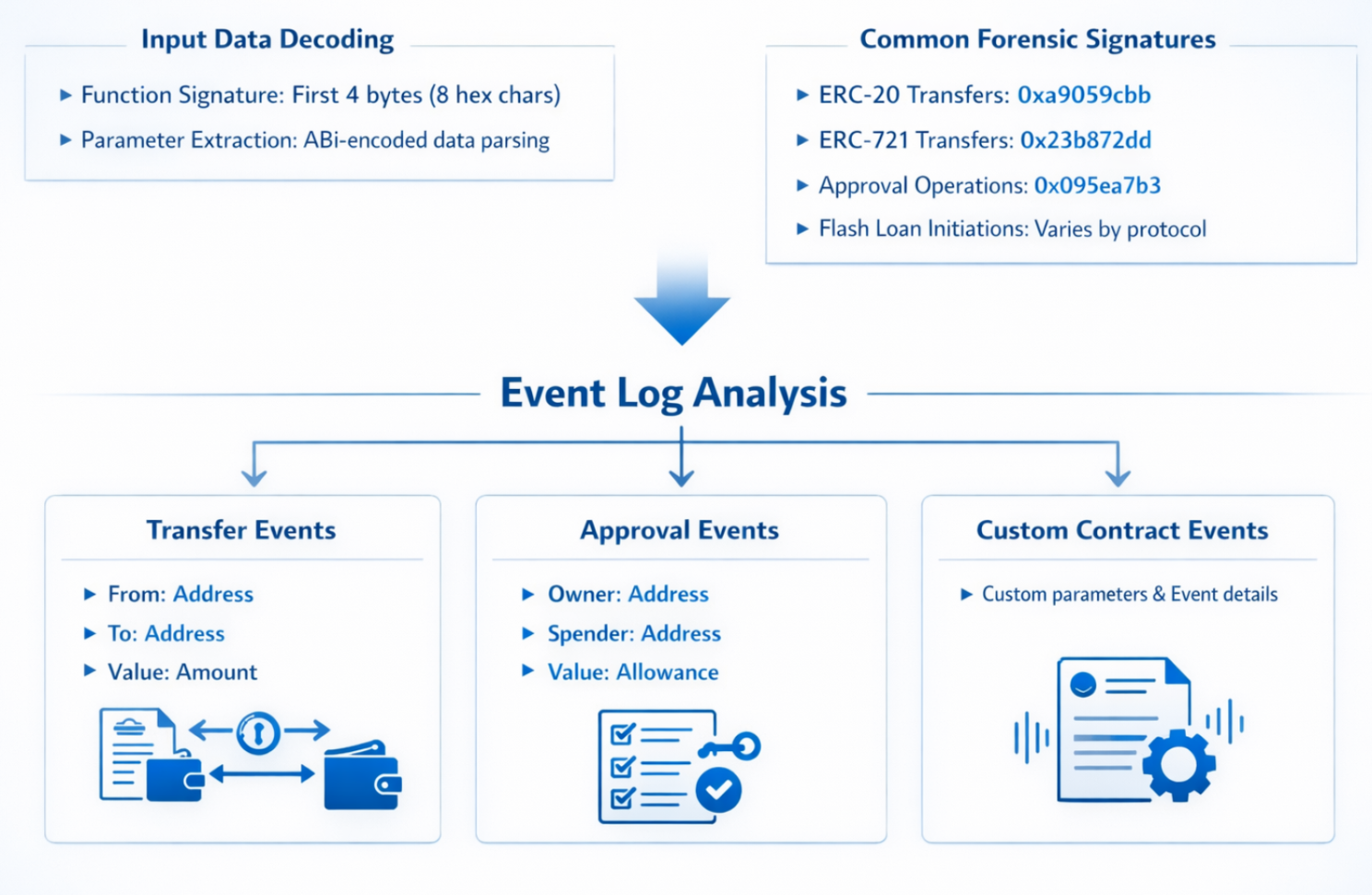
Smart Contract Transaction Forensics
Part 4: Money Laundering Techniques & Counterforensics


NFT-Based Money Laundering – Wash Trading Patterns
Indicators:
- Same seller/buyer addresses
- Rapid buy-sell cycles
- Inflated prices with self-dealing
- Sybil armies for fake liquidity
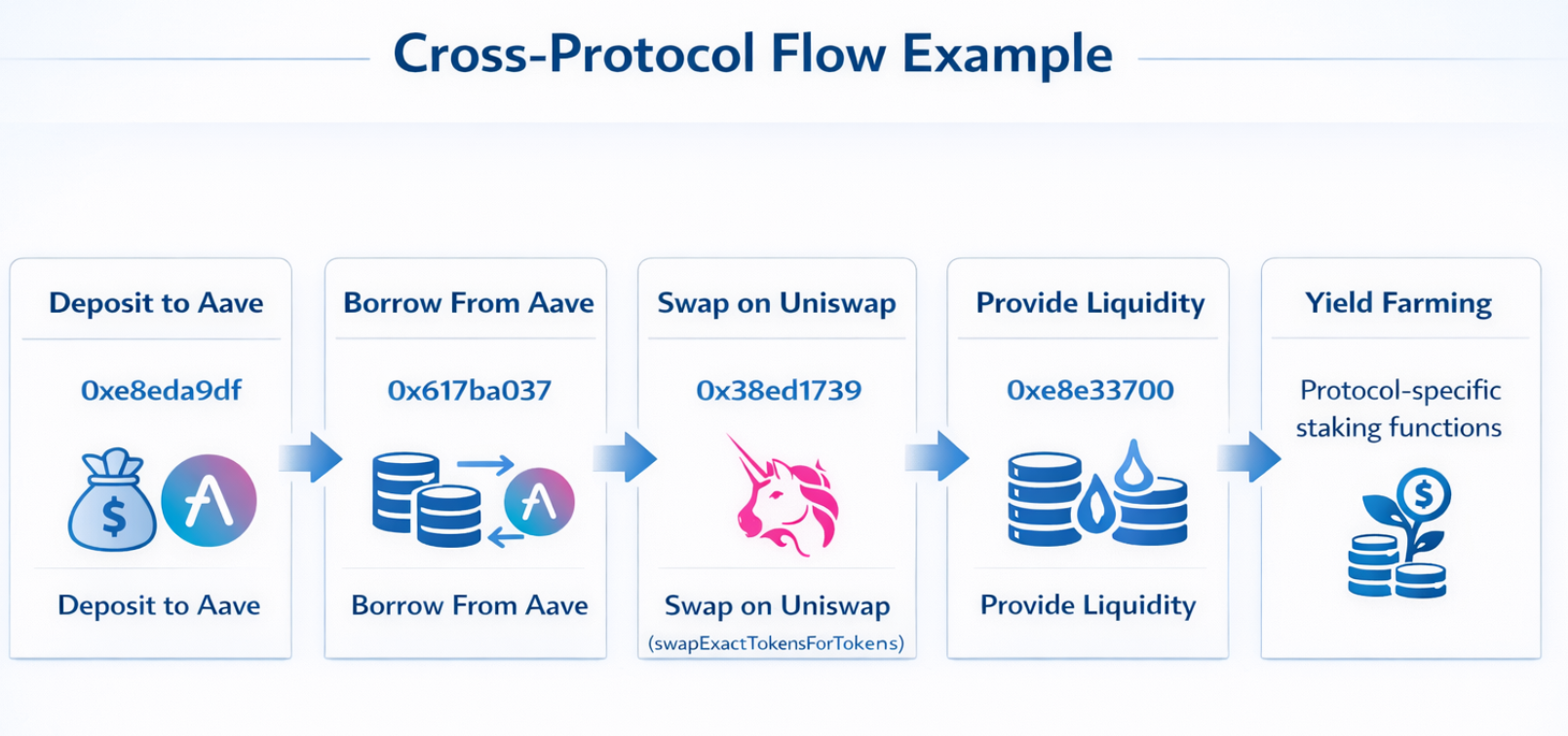
DeFi-Based Laundering

Part 5: Investigative Toolkit & Technical Implementation
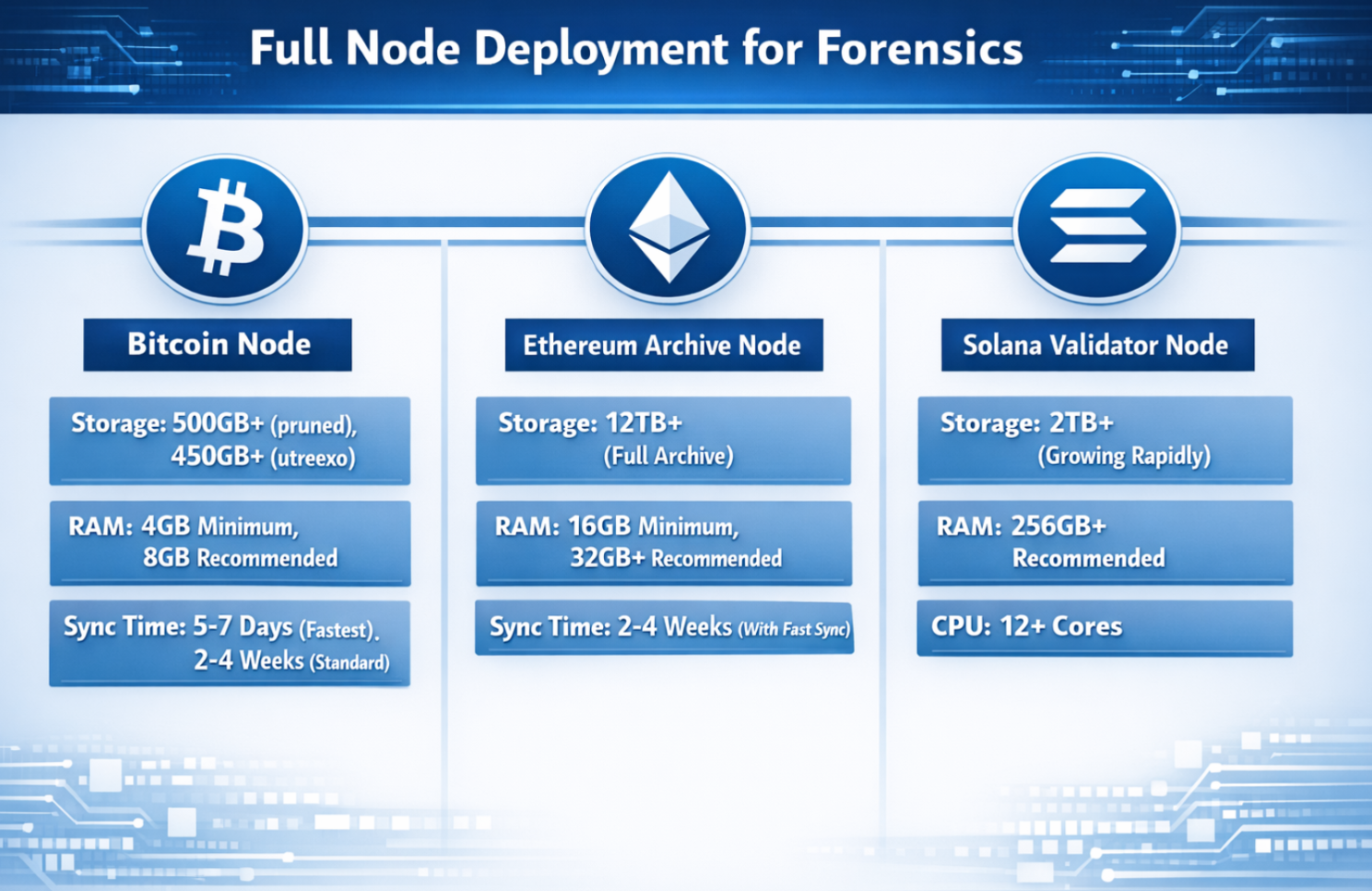
Blockchain Data Acquisition
API Providers: Alchemy, Infura, QuickNode, Blockdaemon, Chainstack, Tenderly, Covalent.
Python Forensic Toolkit Example
from web3 import Web3
import pandas as pd
import networkx as nx
from datetime import datetime
class BlockchainForensics:
def __init__(self, rpc_url):
self.w3 = Web3(Web3.HTTPProvider(rpc_url))
self.graph = nx.DiGraph()
def trace_transaction_flow(self, tx_hash, depth=3):
tx = self.w3.eth.get_transaction(tx_hash)
receipt = self.w3.eth.get_transaction_receipt(tx_hash)
flow_data = {
'from': tx['from'],
'to': tx['to'],
'value': self.w3.fromWei(tx['value'], 'ether'),
'gas_used': receipt['gasUsed'],
'gas_price': self.w3.fromWei(tx['gasPrice'], 'gwei'),
'timestamp': datetime.fromtimestamp(
self.w3.eth.get_block(tx['blockNumber'])['timestamp']
)
}
self.graph.add_edge(tx['from'], tx['to'],
weight=float(tx['value']),
tx_hash=tx_hash.hex())
return flow_data
def detect_mixer_patterns(self, address):
transactions = self.get_all_transactions(address)
mixer_indicators = {
'fixed_amounts': self.check_fixed_amounts(transactions),
'rapid_movement': self.check_temporal_patterns(transactions),
'common_mixer_addresses': self.check_known_mixers(transactions),
'round_number_txs': self.count_round_numbers(transactions)
}
return mixer_indicators
def cluster_addresses(self, address_set):
clusters = {}
for address in address_set:
input_txs = self.get_transactions_with_input(address)
for tx in input_txs:
for inp in tx['inputs']:
if inp not in clusters:
clusters[inp] = set()
clusters[inp].add(address)
return self.merge_clusters(clusters)Graph Database Implementation (Neo4j for Blockchain)
// Create transaction nodes and relationships
CREATE (tx:Transaction {
hash: '0xabc...',
value: 2.5,
gas_price: 45,
timestamp: 1634567890
})
CREATE (from:Address {address: '0x123...'}),
(to:Address {address: '0x456...'})
CREATE (from)-[:SENT {
amount: 2.5,
tx_hash: '0xabc...'
}]->(tx)-[:RECEIVED {
amount: 2.5,
tx_hash: '0xabc...'
}]->(to)
// Query for suspicious patterns
MATCH path = (a:Address)-[:SENT*3..5]->(b:Address)
WHERE a.risk_score > 0.8 AND b.risk_score > 0.8
RETURN path
LIMIT 100;Machine Learning for Anomaly Detection
from sklearn.ensemble import IsolationForest
from sklearn.preprocessing import StandardScaler
import numpy as np
class TransactionAnomalyDetector:
def __init__(self):
self.scaler = StandardScaler()
self.model = IsolationForest(
contamination=0.1,
random_state=42,
n_estimators=100
)
def extract_features(self, transactions):
features = []
for tx in transactions:
feature_vector = [
tx['value'], tx['gas_price'], tx['gas_used'],
self.time_of_day(tx['timestamp']),
self.day_of_week(tx['timestamp']),
len(tx['input_data']) if tx['input_data'] else 0,
self.get_address_age(tx['from']),
self.get_transaction_frequency(tx['from'])
]
features.append(feature_vector)
return np.array(features)
def detect_anomalies(self, transactions):
features = self.extract_features(transactions)
scaled_features = self.scaler.fit_transform(features)
self.model.fit(scaled_features)
predictions = self.model.predict(scaled_features)
anomalies = [tx for tx, pred in zip(transactions, predictions)
if pred == -1]
return anomaliesPart 6: Legal & Regulatory Framework
Global Regulatory Landscape
United States (FinCEN, SEC, CFTC):
- Travel Rule: >$3,000 transfers require beneficiary info
- SAR Reporting: Suspicious Activity Reports required
- OFAC Sanctions: SDN List compliance (Tornado Cash sanction)
European Union (MiCA, 5AMLD, 6AMLD):
- Markets in Crypto-Assets (MiCA): 2024 implementation
- 5AMLD: VASP registration, enhanced due diligence
- 6AMLD: Extended liability, stricter penalties
Law Enforcement Tools & Protocols
Blockchain Analytics for LE: Chainalysis Reactor (90%+ LE agencies), TRM Labs (80+ government agencies), Elliptic (60+ agencies).
Asset Recovery Success Rates (2022):
- Total stolen: $3.8B
- Recovered: $1.9B (50% recovery rate)
- Highest recovery: Nomad Bridge (90%+)
- Lowest recovery: Ronin Bridge (<10%)
Part 7: Case Studies & Real-World Investigations
Bitfinex Hack 2016 ($4.5B Bitcoin Recovery 2022)
Forensic Techniques: blockchain clustering, exchange KYC correlation, cloud storage metadata analysis, transaction timing correlation. Outcome: DOJ arrested couple, seized 94,000 BTC.
Poly Network Hack 2021 ($611M, Fully Recovered)
Attack vector: contract vulnerability. Recovery: hacker communicated via embedded transactions, returned funds gradually, received white hat bounty.
Ronin Bridge Hack 2022 ($625M)
Attack: compromised 5/9 multi-sig validator nodes via social engineering. Attribution: North Korean Lazarus Group, used Tornado Cash mixer. US Treasury sanctioned mixer addresses.
The Twitter Hack 2020 Investigation
Attack: high-profile Twitter accounts compromised, Bitcoin scam addresses posted, $118,000 received. Forensic analysis identified 3 primary addresses, exchange withdrawals traced. Outcome: Florida teenager arrested, funds seized.
Part 8: Future Trends & Emerging Threats
Quantum Computing Threats
Vulnerable primitives: ECDSA (Bitcoin/Ethereum signatures), RSA. Timeline: 2025-2030 early advantage possible, 2030-2040 practical quantum computers expected. Migration strategies: post-quantum cryptography, quantum-resistant signatures, quantum key distribution.
AI/ML in Crypto Forensics
Emerging applications: predictive analytics, automated investigation, deep learning for graph neural networks, neural style detection for mixing patterns.
Privacy-Enhancing Technology Evolution
Next-generation: Fully Homomorphic Encryption (FHE), Multi-Party Computation (MPC), Zero-Knowledge Everything (zkEVMs). Forensic challenges: complete transaction privacy, only proof verification possible.
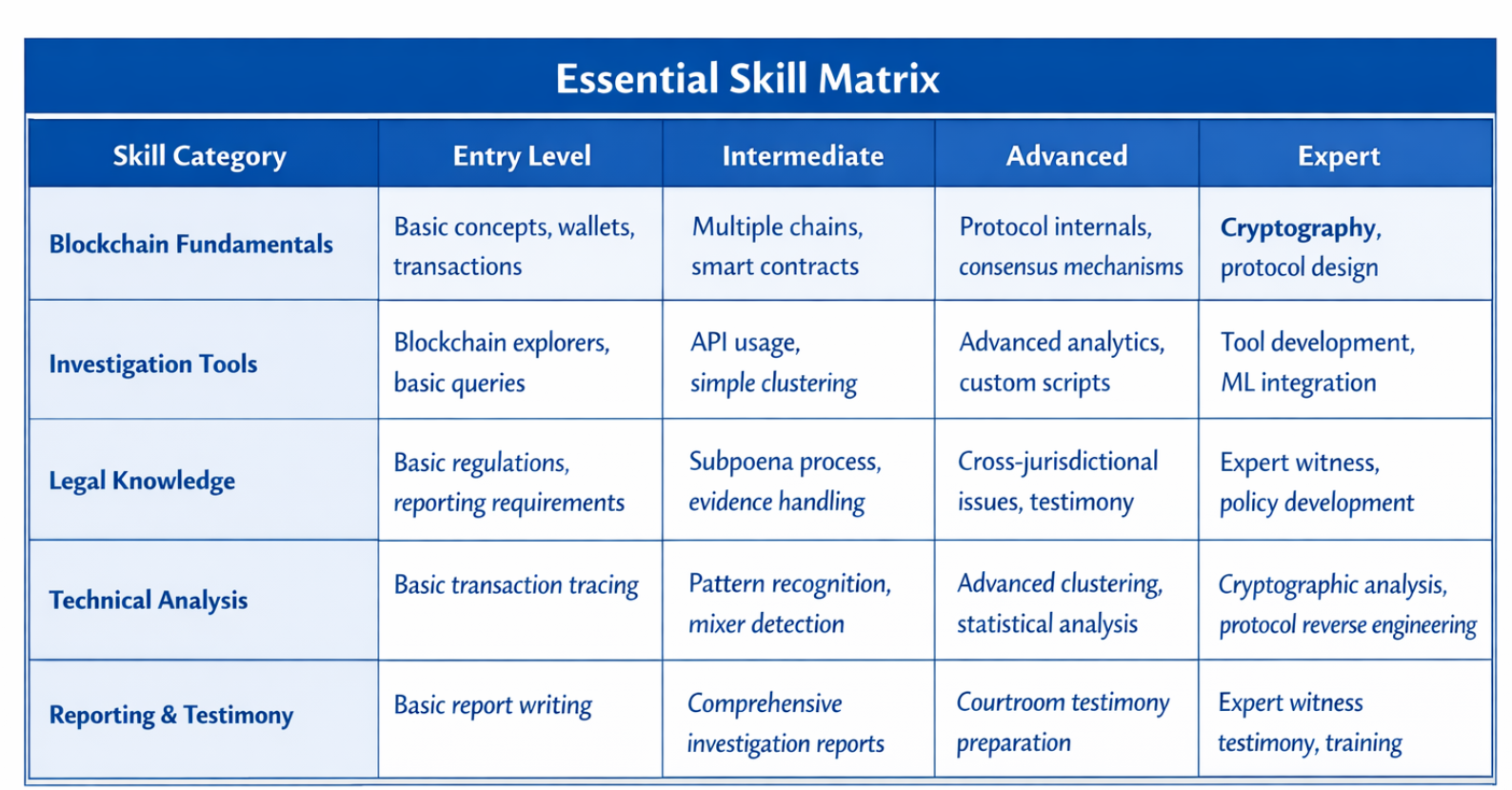
Part 9: Professional Certifications & Training
Industry Certifications
- Chainalysis Reactor Certification (CRC)
- CipherTrace Examiner Certification (CTEC)
- Blockchain Forensic Investigator (BFI)
Essential Skill Matrix
Part 10: Best Practices & Operational Framework
Investigative Best Practices
Evidence Preservation Protocol:
- Capture screenshots with timestamp, record blockchain explorer URLs
- Hash all digital evidence, use write-blockers, maintain logs
Multi-Agency Collaboration Framework:
- SARs, FinCEN Exchange meetings, joint task forces
- Standardized data formats, secure communication, jurisdictional agreements
Proactive Defense Strategies
Exchange & VASP Security: real-time screening, customer risk scoring, known bad address screening, KYC/CDD enhancements, multi-sig wallets, rate limiting, address whitelisting.
Individual User Protection: hardware wallet, multi-factor authentication, separate addresses, regular smart contract audits.
Conclusion
The Evolving Battlefield: Blockchain security and crypto forensics represent a constantly evolving cat-and-mouse game. Key takeaways:
- Sophistication Gap is Narrowing: Forensic tools are catching up
- Regulation is Accelerating: Global frameworks maturing
- Cross-chain is the New Frontier: Investigations must span ecosystems
- Professionalization of Field: Certifications emerging
The field requires continuous learning and adaptation. Success depends on technical expertise, legal knowledge, and investigative creativity working in concert.
Disclaimer: The content shared here is strictly for learning and research purposes to understand the fundamentals and advanced concepts of crypto forensic tools and investigation methodology. This does not encourage or support any unauthorized blockchain monitoring, hacking, or illegal activity.
Case Studies
Empowering Digital
Evolution
Blogs
Empowering Digital
Evolution
BitViraj Technologies - Your Gateway to
Tomorrow's Innovations
Embark on a DigitalJourney


The next-generation digital technology company Bitviraj has the potential to empower and reinvent business in the current fast-paced market.
Our Service
- Website Development
- Application Development
- Blockchain Development
- Gaming and Metaverse